Login Form
Poly-Asia - Shopping cart
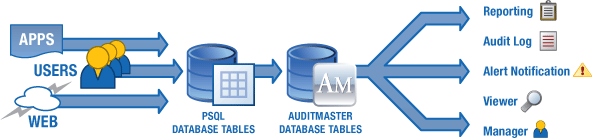
AuditMaster Technology
Pervasive AuditMaster provides compliancy and transaction monitoring of your critical applications and processes so you'll always know who's doing what to your data when, where and how.
AuditMaster has three components:
- Log event handler
- Log database
- Log viewer
The log event handler is an easily installed database plug-in. It serves as an all-seeing flight recorder, writing every qualifying database event into the audit trail. It's installed at the database level, so when the database is running, the event handler is running, keeping the audit trail complete. The log event handler is installed on the system with the Pervasive PSQL server engine.
The log database is a set of Pervasive PSQL files in their own directory. The main log file holds all audit information, such as user ID, network station ID, time and date of operation, application name, database table name, and operation type.
The log file also includes before-and-after transaction images for updated records. Each time a user changes data, the log event handler writes both the original and the new record to the log.
The log viewer queries the log database, enabling a security administrator to verify past activities or analyze patterns and trends. A graphical interface simplifies rapid building of queries. AuditMaster reports can also supply evidence of compliance with best or required corporate security practices. In addition, the log viewer component is used to maintain and configure the AuditMaster system.
AuditMaster Alerts
Administrators can create alerts customized to their business rules. Once defined, alerts wait for specific events of interest based on the entire range of user actions, including creating, updating and deleting data, or even simply reading it. When a watched-for event occurs, the log event handler immediately executes an alert, which can take the form of an email to one or more recipients, a call to another application, or the start-up of a new application. The log viewer may be installed on any machine with access to the Pervasive PSQL server and log database files.
